Resource access reports
Resource access covers the transfer of users to resources.
These statistics are based on a user being transferred to a resource as part of an authentication / authorisation event. They cannot show what the user did on that publisher's site, and because they can only record the transfer to the resource when the resource sends the user to us as part of a sign-in, they might not match up exactly with what a publisher reports - for example their stats might also include IP authorised users. Because of this, some sites take the view that IP auth should be disabled.
Common elements are described on the data explorer page.
Any report you generate can be saved to your computer or scheduled, very useful if you have a lot of data that won't fit on the screen.
Scope | This organisation All organisations |
Granularity | Hourly Daily Monthly |
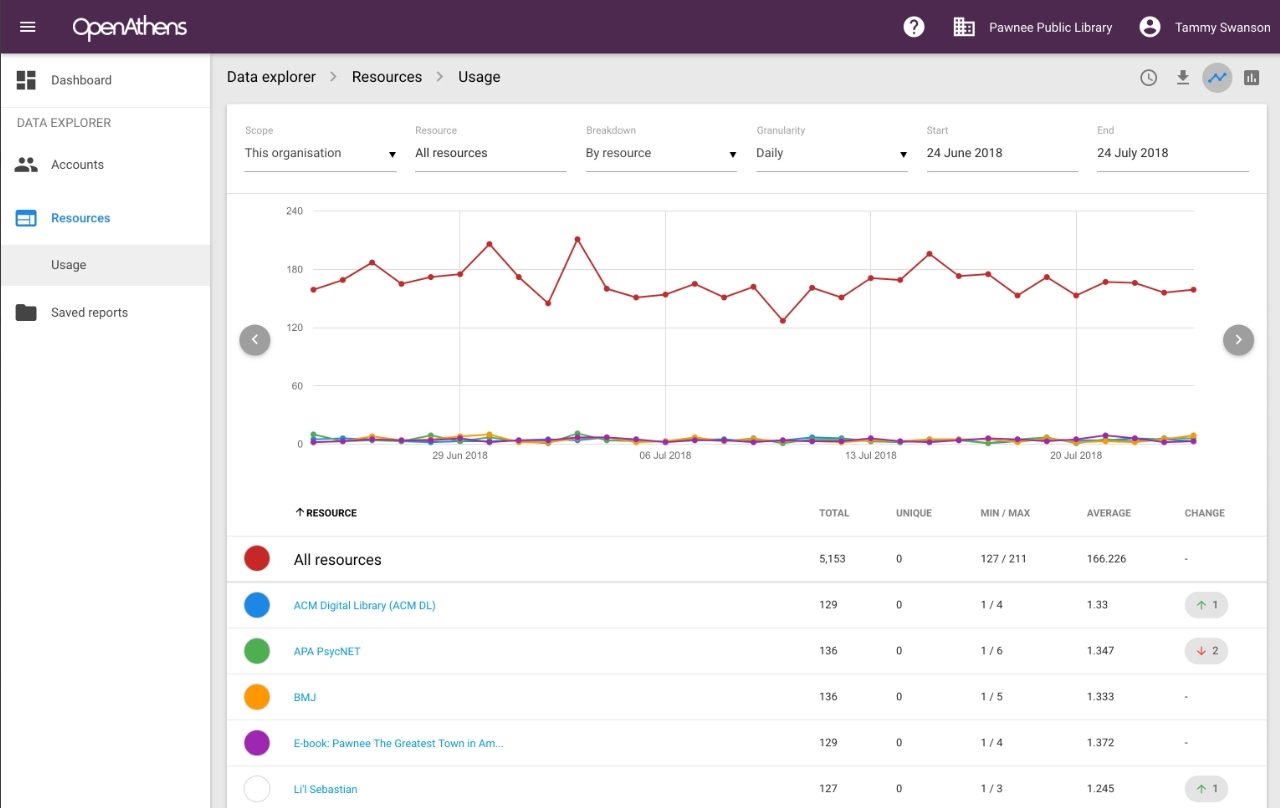
Breakdowns
By resource - the resources accessed.
By group - the user groups assigned to users who were transferred to resources. Not available across organisations.
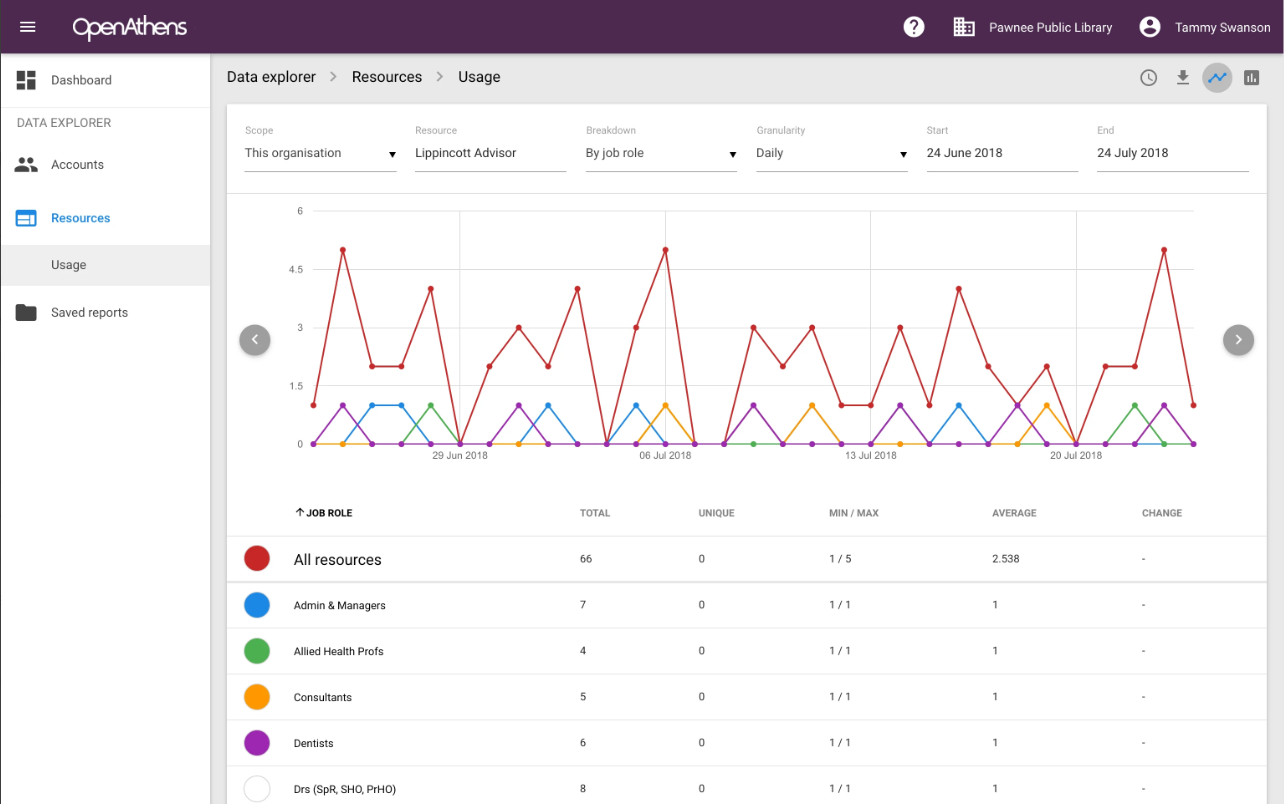
By permission set - the permission sets assigned to users who were transferred to resources. Not available across organisations. Permission sets are reported whether or not they contain the resource in question.
By custom attribute - any custom attribute you have added to your schema and marked as reportable.
These breakdowns can be viewed for all resources or a single resource by selecting a resource from the dropdown at the top of the page or clicking on a resource name on the all resources view.
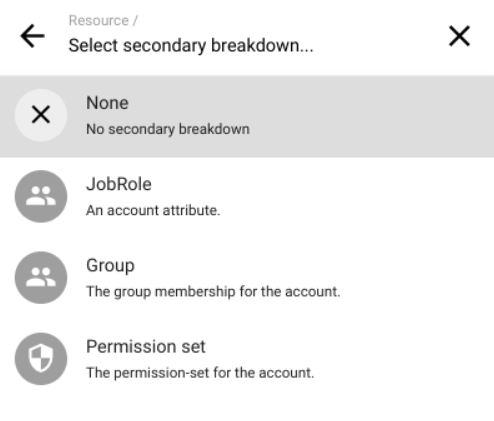
Secondary breakdown
If you select resource as the breakdown, you will be presented with an option to select an additional breakdown - e.g. permission set, group or any reportable attribute. As this can make the interface a little crowded, downloading the report may be helpful.
Anything to watch out for?
Some attributes can have multiple values for a single user. When analysing these attributes, the total count can be higher than the number of users because each user action is counted for every applicable value.
A good example are permission sets, where the key connection is the user, not the resource. This means you might see statistics for a permission set related to a resource even if that resource isn't directly assigned to the set. This happens when users have other sets that include the resource.
If you need to combine or include additional breakdowns to those available in the interface, you will need to access the raw data via API - this is an optional extra and your account manager will be happy to discuss it with you.
