Sign in to Adobe Creative Cloud Enterprise with OpenAthens
This is an example using Adobe Creative Cloud Enterprise of how to set up a custom SAML resource so that you can log in using OpenAthens.
Prerequisites
- Access to the Adobe enterprise dashboard
- Some test users already set up in the Adobe dashboard as federated
- Access to your the OpenAthens administration area as the domain administrator
Method
Configure Adobe enterprise dashboard
- Under the identity section, claim your domain. Follow their instructions (should be linked from the identity section). This can take a while as you need to add a token to your DNS record for automatic validation and then wait for manual verification.
- Once claimed you can
Upload your IdP certificate. This is the x509 signing certificate from your metadata. Copy and paste it into a file as follows including the begin and end parts:
IDP Issuer = your entityID, e.g. https://idp.example.com/openathens. View on the organisation summary.
IDP login URL = your SAML 2 sso address e.g. https://login.openathens.net/saml/2/sso/Your_API_name
IDP binding: select HTTP-REDIRECT
User Login Setting: This guide uses email address, but choose what matches the users you have set up in the dashboard.
Download metadata. Do so and save it for later (the download doesn't work in Firefox at the time of writing)
Configure OpenAthens
Add custom SAML resource
Like Google, Adobe are not members of a common federation so we need to add them as a custom SAML resource.
- Go to Resources > Catalogue > Custom > Add > SAML
- Upload the metadata file you downloaded from the Adobe dashboard
- Optionally rename the new custom resource (click on the resource name, edit and save).
Map attributes (if you have a local connection)
If you have a local connection and you are not already mapping email address, first name and last name to OpenAthens attributes you will need to set up additional mappings. This is done on the attributes tab of your connection, see: Attribute mapping .
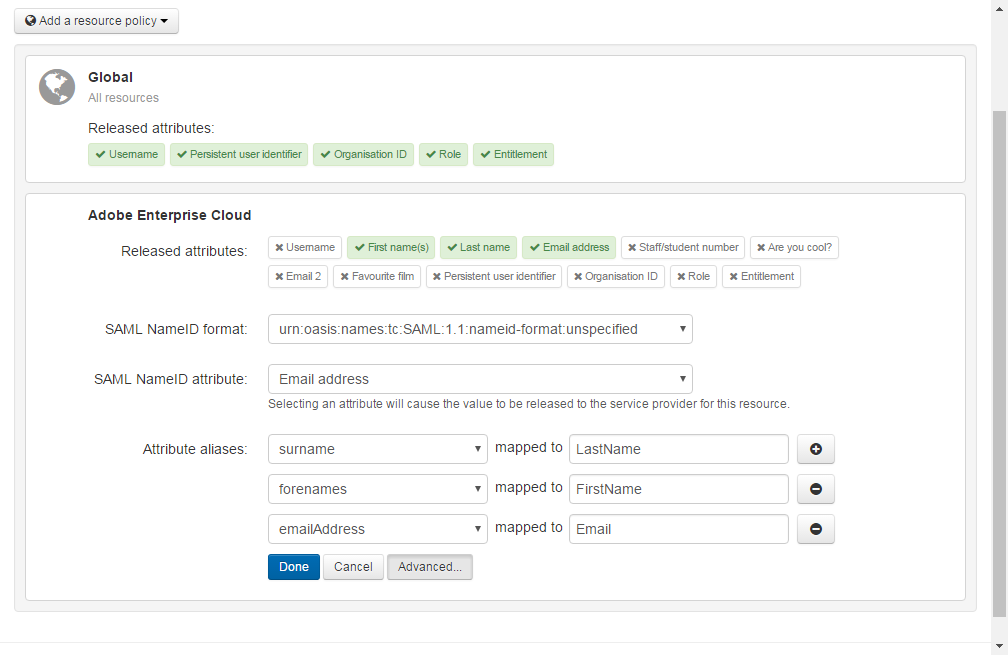
Release policy
The final step is to release those attributes to Adobe and this is controlled by the release policy.
- Go to Preferences > Attribute release.
- Add a new policy and search for the name of your custom SAML resource
- Click on first name, last name and email address to add them to the policy.
- Click advanced
- Leave the SAML NameID format as unspecified
- Set the SAML NamdID attribute as 'Email address'
- Add the following aliases
- forenames mapped to FirstName
- surname mapped to LastName
- emailAddress mapped to Email
- Leave the SAML NameID format as unspecified
- Click Done and then Save changes.
Test
Go to Adobe and enter the email address of a user who is configured at the Adobe end to use a federated login. You should be transferred to your OpenAthens login. Once you have signed in there you should be transferred back to Adobe and logged in.
Anything to watch out for?
If you are running in restrictive mode:
- The SAML resource MUST be included in at least one of the permission sets used by anyone who should gain access. If not, OpenAthens will block access at the authentication point.
- If you have sub-organisations you MUST ALSO allocate the custom resource to permission sets under those sub-organisations. The cascade option may be useful.
Whilst our service desk will always try to be helpful, they can only support the OpenAthens part of this.
